The rapid evolution of technology and the global shift in workplace dynamics have made remote work a staple in the professional world. As beneficial as it is, this new norm comes with its set of challenges, particularly in maintaining robust security. Securing remote work requires a multifaceted approach that adapts to changing technologies and diversifying threats. This article delves into the various aspects of remote work security, highlighting strategies and technologies that can protect teams across the globe.
Understanding the Importance of Remote Work Security
Remote work security is more critical than ever. With employees accessing company resources from diverse locations, ensuring data security is a top priority. In a traditional office setting, security measures like firewalls and on-premises IT support can mitigate risks directly. However, remote environments lack these physical controls, making digital security practices essential. Companies must navigate the fine line between accessibility and security without compromising sensitive information.
The expanding landscape of cybersecurity threats targets remote workers directly. Cyber attackers use sophisticated methods to penetrate systems, exploiting vulnerabilities inherent to remote setups. These include phishing attacks, unsecured Wi-Fi networks, and inadequate personal device security. Organizations adopting remote work must adopt comprehensive security protocols to safeguard against data breaches and cyber threats.
Challenges in Securing Remote Work
The rise of remote work brings unique challenges that require innovative solutions. Identifying these challenges is the first step in establishing robust security protocols.
Cybersecurity Threats
Cybersecurity threats have grown more complex with remote work. Phishing attacks are particularly prevalent, often disguised as legitimate work-related emails. Unsuspecting employees can fall victim to these schemes, compromising data integrity.
Unsecured Networks
Remote work typically involves employees connecting to unsecured networks, such as public Wi-Fi, which are vulnerable to cyber attacks. Hackers can intercept data transmitted over these networks with relative ease.
Personal Device Usage
Many remote employees use personal devices, which may lack appropriate security controls, increasing the risk of data breaches. Company data and personal data often intermingle, complicating security measures.
Scalability Issues
Securing an expanding remote workforce presents scalability issues. Solutions that work for a small number of employees may not be suitable or affordable as the workforce grows.
Lack of IT Support
In traditional workplaces, IT departments offer immediate response to security issues. Remote work environments can lack this immediacy, delaying responses to critical security incidents.
Strategies for Securing Remote Work
Addressing the security challenges of remote work requires proactive strategies and technologies tailored to safeguard digital environments. Companies must build a culture of security awareness among their remote teams.
Implementing Strong Password Policies
Strong passwords are a critical first line of defense against unauthorized access. Organizations should enforce password policies requiring regular updates and complexity. Multi-factor authentication (MFA) adds an additional security layer, making it more difficult for unauthorized users to gain access.
Using Virtual Private Networks (VPNs)
VPNs encrypt the data traveling between remote workers and company servers, enhancing security on unsecured networks. VPNs are crucial for protecting sensitive information from eavesdropping, particularly for employees who frequently access public Wi-Fi.
Endpoint Security Solutions
Endpoint security solutions monitor and protect devices connecting to the company network. These solutions can detect unusual activities and block malicious actions before they compromise security. Anti-virus software, firewalls, and intrusion detection systems form vital components of endpoint security.
Data Encryption
Encrypting data ensures that, even if intercepted, it remains inaccessible without the correct decryption key. Remote work policies should mandate encryption for all data both in transit and at rest.
Regular Security Training
Educating employees on security best practices is crucial. Regular training sessions can help reduce the risk of human error, which is often the weakest link in security chains. Training should include recognizing phishing attempts, handling data securely, and understanding company security policies.
Cloud Security Practices
The use of cloud-based applications makes securing cloud environments essential. Implementing appropriate access controls, monitoring user activities, and maintaining compliance with industry standards are integral to cloud security.
The Role of Technology in Enhancing Remote Work Security
Technology plays a critical role in safeguarding remote work environments. Tools and platforms designed with security in mind can mitigate risks effectively, allowing companies to operate confidently.
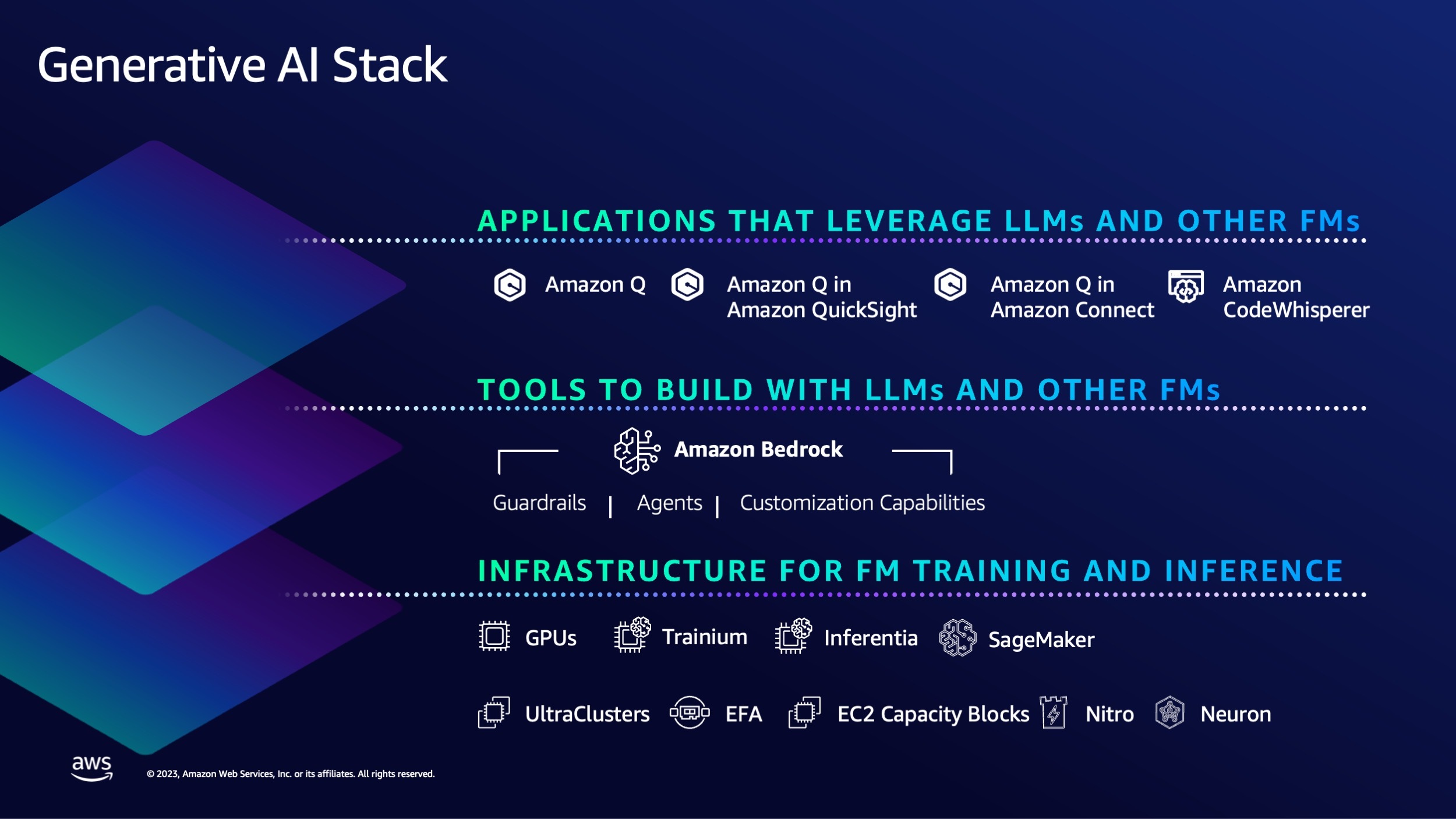
Advancements in Artificial Intelligence (AI)
AI-powered security solutions offer proactive threat detection and response capabilities. By analyzing patterns and identifying anomalies, AI can flag potential security breaches in real-time, allowing companies to act swiftly.
Automation in Security Processes
Automating security processes can improve efficiency and reduce human error. From patch management to security monitoring, automation ensures consistent adherence to best practices without overburdening IT teams.
Zero Trust Architecture
Adopting a zero trust architecture means that no user is trusted by default, whether inside or outside the organization’s network. Verification is required from everyone, reinforcing security by validating users each time they seek access.
Secure Access Service Edge (SASE)
SASE combines network security functions with WAN capabilities, allowing secure access to applications, regardless of user location. It is a comprehensive approach for securing remote work by integrating flexible and scalable security solutions at the network edge.
Building a Culture of Security Awareness
A culture of security awareness empowers employees to serve as the first line of defense against cybersecurity threats. Companies must cultivate an environment where security is integrated into everyday responsibilities, making everyone accountable for protecting digital assets.
Leadership Involvement
Leaders play a pivotal role in promoting security practices by setting the standard and ensuring that resources are allocated for security initiatives. Communicating the importance of security from the top down establishes its significance within the organization’s culture.
Employee Engagement
Creating opportunities for employees to engage with security topics fosters acceptance and understanding. Interactive workshops and discussions on recent security trends and incidents keep employees informed and vigilant.
The Future of Remote Work Security
As remote work becomes increasingly entrenched in the professional landscape, so too will the evolution of security practices. The future promises continued technological advancements, necessitating adaptive and forward-thinking approaches to cybersecurity.
Evolving Cyber Threats
Cyber threats will continue to evolve, becoming more sophisticated and elusive. Future security measures will require innovation and agility to outpace these threats and maintain robust defenses.
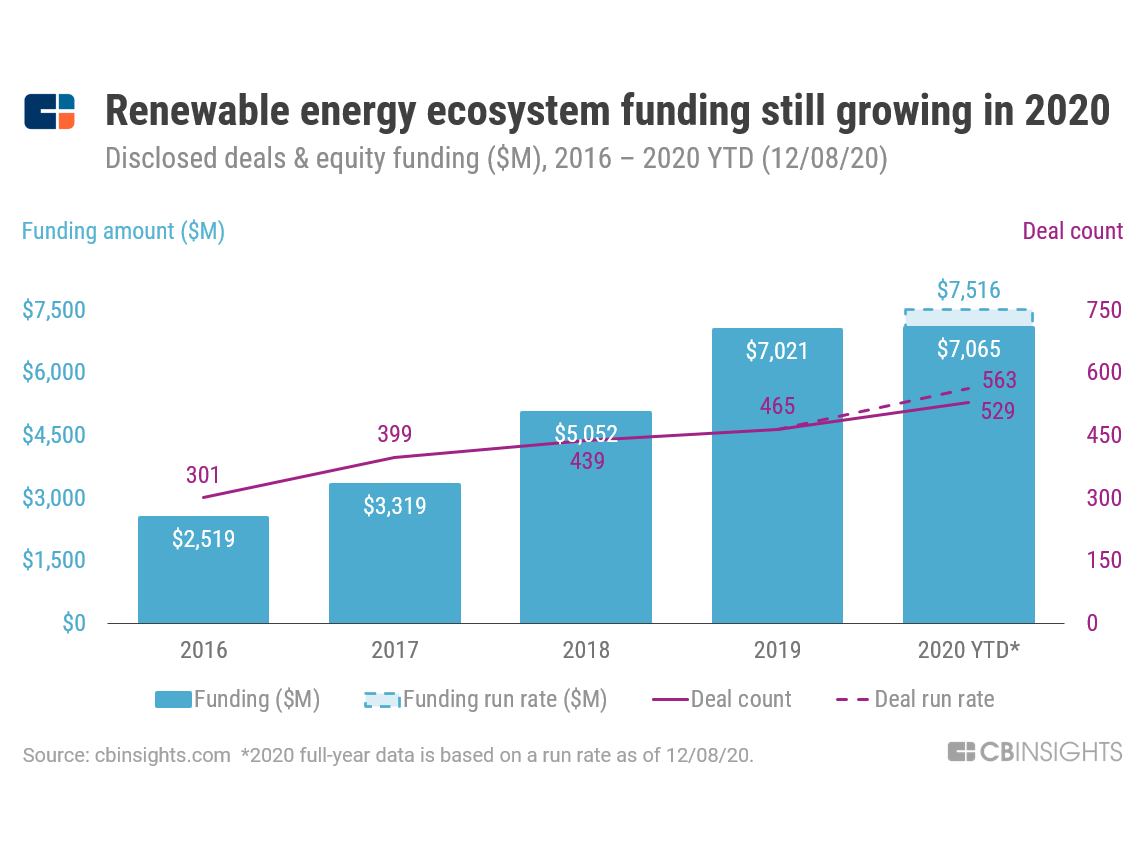
Investment in Cybersecurity
Organizations must prioritize investment in cutting-edge cybersecurity solutions and infrastructure. This investment not only protects current operations but also positions companies to take advantage of future digital opportunities securely.
Personalized Security Solutions
The one-size-fits-all model is insufficient for diverse organizations. Personalized security solutions tailored to specific organizational needs will better address the unique challenges faced by remote workers.
Conclusion
Securing remote work in the digital age demands a comprehensive approach that integrates technology, policy, and culture. Organizations must remain vigilant, continuously adapting to new threats while fostering an environment where security is everyone’s responsibility. By prioritizing “securing remote work,” companies can protect their digital assets, ensuring operational continuity and future growth in an increasingly digital-first world.
| Strategy | Description |
| Strong Password Policies | Enforce complex password requirements and implement multi-factor authentication for enhanced security. |
| VPN Usage | Protect data through encryption when accessed over unsecured networks. |
| Endpoint Security Solutions | Provide constant monitoring and blocking of unauthorized activities on remote devices. |
| Data Encryption | Ensure that data remains encrypted both in transit and at rest to prevent unauthorized access. |
| Cloud Security Practices | Implement access controls and maintain compliance standards to secure cloud-based services and applications. |